Serverless Authorization: A Practical Guide
Serverless computing is a cloud computing model that allows you to build and run applications without worrying about infrastructure management. With serverless architecture, you don't need to provision and manage servers. Instead, you can focus on writing code and deploying it to a cloud provider that takes care of everything else.
Serverless computing is becoming increasingly popular due to its flexibility and cost-effectiveness. However, serverless architecture presents a unique set of security challenges that you need to address. One of the most important aspects of serverless security is authorization.
What is Serverless Authorization?
Serverless authorization is the process of granting or denying access to serverless application resources based on user identity and permissions. It ensures that only authorized users can access your application's resources, such as databases, APIs, and storage.
Serverless authorization is crucial for securing serverless applications. It prevents unauthorized users from accessing your resources, which can result in data breaches, unauthorized data access, and other security issues.
Implementing Serverless Authorization
Implementing serverless authorization can be done using various approaches. The choice of approach depends on the requirements of your application and the cloud provider you are using. Here are some of the most common approaches to serverless authorization.
Approach 1: API Gateway and Lambda Authorizers
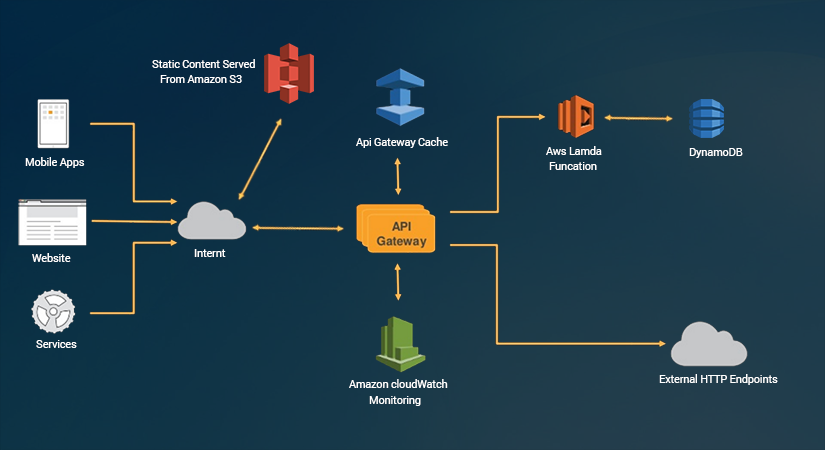
API Gateway and Lambda Authorizers are popular approaches to serverless authorization. This approach involves using API Gateway to authenticate and authorize users, and Lambda functions to implement authorization logic.
API Gateway is a fully managed service that makes it easy to create, publish, maintain, monitor, and secure APIs at any scale. Lambda Authorizers are Lambda functions that API Gateway calls to authenticate and authorize requests before they reach the backend.
Using API Gateway and Lambda Authorizers, you can create a custom authorization logic that suits your application's requirements. This approach is flexible and scalable and can handle complex authorization scenarios.
Approach 2: AWS Cognito
AWS Cognito is a user authentication and authorization service that makes it easy to add user sign-up, sign-in, and access control to your web and mobile apps. It provides a simple and secure way to authenticate and authorize users using standard identity providers, such as Amazon, Facebook, Google, and Apple.
AWS Cognito integrates with API Gateway, Lambda, and other AWS services to provide a comprehensive serverless authorization solution. It also provides features such as user management, multi-factor authentication, and user pool federation.
Using AWS Cognito, you can implement user authentication and authorization with minimal effort. It's a cost-effective and scalable solution that can handle millions of users.
Approach 3: Auth0
Auth0 is a cloud-based identity platform that provides authentication and authorization as a service. It supports standard identity providers, such as Facebook, Google, and Microsoft, as well as custom identity providers.
Auth0 integrates with serverless architectures to provide a comprehensive authorization solution. It provides features such as user management, social login, and multi-factor authentication.
Using Auth0, you can implement user authentication and authorization with minimal effort. It's a scalable and secure solution that can handle millions of users.



